Introduction: 2026 – The Year Banking Fraud Industrialized
Banking scams in 2026 are no longer isolated fraud attempts. They operate like structured businesses. Organized crime syndicates now combine artificial intelligence, cross-border money laundering, crypto wallets, instant payment rails, insider collusion, and psychological manipulation to extract massive sums from victims.
Fraud has evolved in three major ways:
- Scale – Global operations targeting thousands simultaneously.
- Speed – Instant payment systems reduce recovery windows.
- Sophistication – AI, deepfakes, and synthetic identities bypass traditional controls.
Below is a complete breakdown of the 20 largest and most impactful banking scams of 2026, with detailed explanations, real-world examples, and actionable protection measures.
1. Transnational Scam Compounds (“Scam Parks”) – Southeast Asia



What It Is
Industrial-scale fraud centers operating like corporate campuses.
How It Works
Victims are contacted via dating apps or social platforms. After weeks of emotional trust-building, they are introduced to fake crypto or investment platforms. Funds are routed through multiple bank accounts and converted to crypto.
Financial Impact
Losses often run into hundreds of millions globally due to centralized operations.
Real Example
Reuters investigation into Cambodia scam compound:
https://www.reuters.com/world/china/scammers-abandoned-cambodia-compound-exposes-brutality-banality-fraud-2026-02-06/
How to Stay Safe
• Verify investment platforms independently.
• Avoid financial decisions based on online-only relationships.
• Be cautious of guaranteed high returns.
2. Authorized Push Payment (APP) Fraud
What It Is
Victims are tricked into sending money themselves.
How It Works
Scammers impersonate bank officials or government agencies and create urgency. Since the victim authorizes the transaction, recovery becomes difficult.
Financial Impact
APP fraud remains one of the highest loss categories in developed banking systems.
Real Example
Guardian investigation into refund disputes:
https://www.theguardian.com/money/2026/feb/07/monzo-natwest-hsbc-refunds-fraud-scam-fos-ombudsman
Prevention
• Banks never ask you to move money to a “safe account.”
• Use verification-of-payee tools.
3. ATM Cash Van Heists

What It Is
Physical robbery of vehicles transporting ATM cash.
How It Works
Criminals use insider tips or impersonate officials to intercept cash vans.
Financial Impact
Individual robberies can exceed several crores.
Example
NDTV Bengaluru case:
https://www.ndtv.com/india-news/bengaluru-cash-van-heist-case-cracked-3-arrested-rs-5-76-crore-recovered-9681356
Prevention
• Route randomization.
• Background verification of logistics staff.
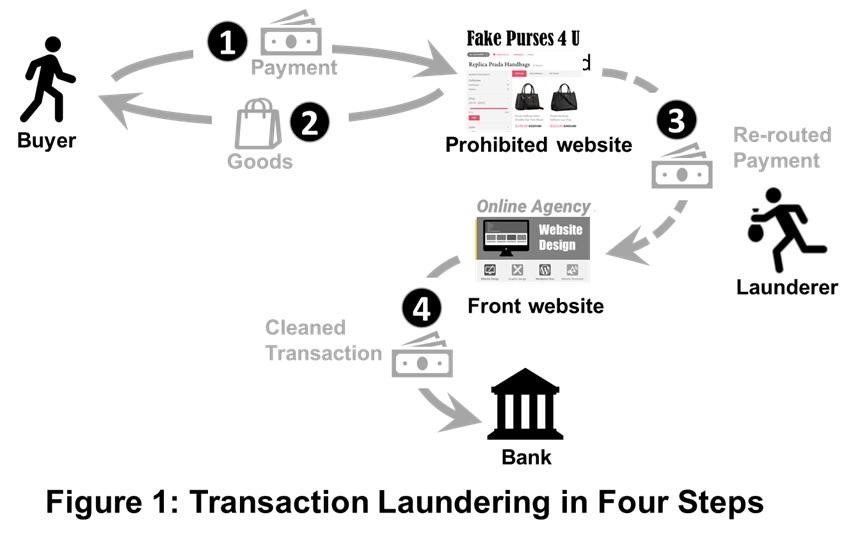
4. Money Mule Networks
What It Is
Using third-party accounts to move stolen funds.
How It Works
Fraudsters recruit people via job offers to “rent” bank accounts. Money passes through layers to hide origin.
Example
Times of India mule account crackdown:
https://timesofindia.indiatimes.com/city/bengaluru/cyber-command-cracks-down-on-mule-accounts-13-arrested/articleshow/128005065.cms
Prevention
• Never share account access.
• Report suspicious deposits immediately.
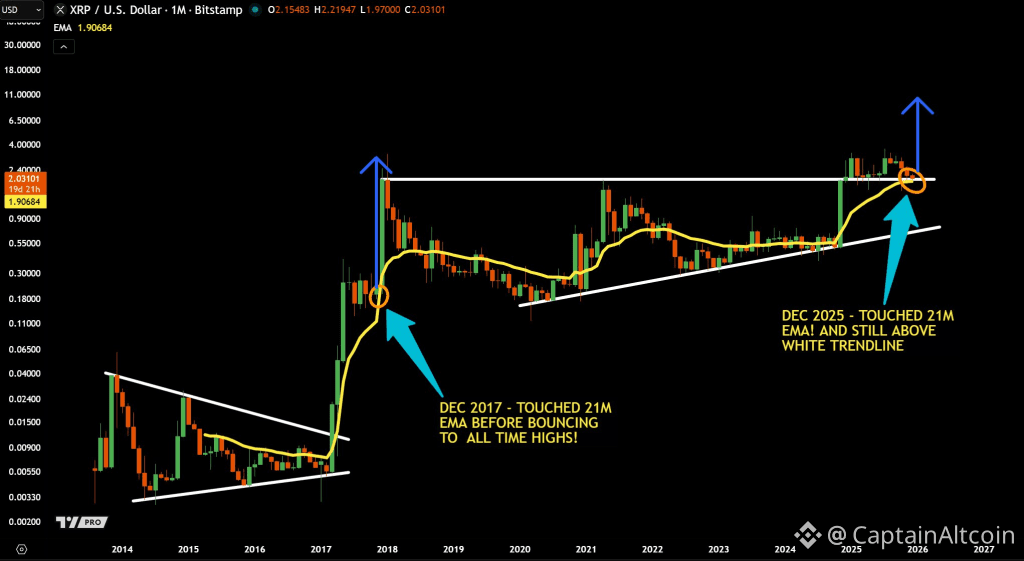
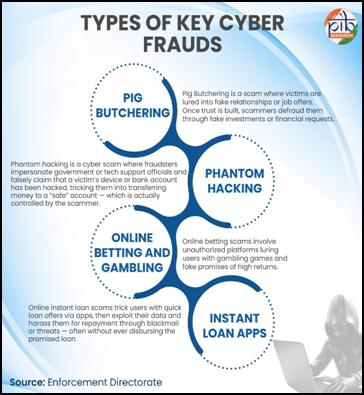
5. Pig-Butchering Crypto Scams
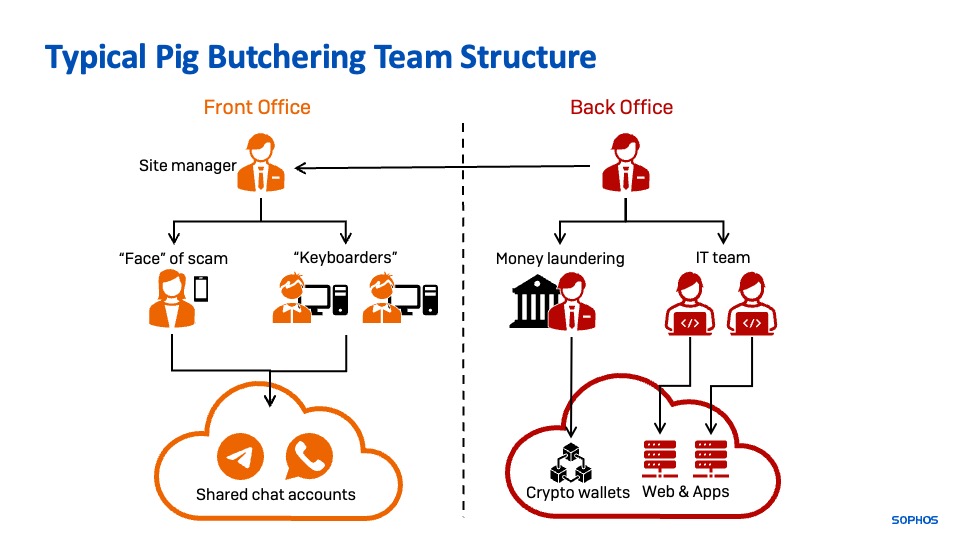



What It Is
Long-term emotional manipulation before fake investment pitches.
How It Works
Victims see fake profits and invest more. Withdrawals are blocked unless “tax” is paid.
Example
Chainalysis report:
https://www.chainalysis.com/blog/crypto-scams-2026/
Prevention
• Avoid unknown crypto platforms.
• Verify regulatory registration.
6. Deepfake Voice Fraud Targeting Banks




What This Scam Is
Deepfake voice fraud is one of the fastest-growing banking threats in 2026. It involves criminals using artificial intelligence to clone a person’s voice and impersonate them convincingly over phone calls.
Unlike traditional phishing, this scam bypasses emotional suspicion because the victim or bank employee believes they are speaking to a known individual.
How the Scam Works – Step by Step
- Voice Data Collection
Fraudsters gather voice samples from social media videos, podcasts, webinars, or leaked recordings. - AI Voice Cloning
AI software generates a realistic synthetic version of the target’s voice. - Targeted Call Execution
Criminals call a bank, finance department, or employee posing as a senior executive or account holder. - Urgent Financial Instruction
The fake “executive” requests an immediate fund transfer or confidential data access. - Funds Transferred
Because the voice sounds authentic, verification controls are bypassed.
Why It Is So Effective
• Humans trust familiar voices
• Traditional voice verification fails
• Urgency creates psychological pressure
• Works even in companies with email verification
Real Example
Mastercard fraud trends report on AI-driven scams:
https://www.mastercard.com/global/en/news-and-trends/stories/2026/the-rise-of-scams.html
Financial Impact
Deepfake fraud incidents have resulted in multi-million dollar corporate wire losses globally. The damage is amplified because detection often happens only after reconciliation.
How to Stay Safe
For Banks & Corporates:
• Never rely solely on voice verification
• Mandatory callback to verified number for large transfers
• Multi-person authorization for high-value payments
• Behavioral transaction monitoring
For Individuals:
• Avoid sharing lengthy voice recordings publicly
• Be cautious if a known contact urgently asks for money
7. Business Email Compromise (BEC)
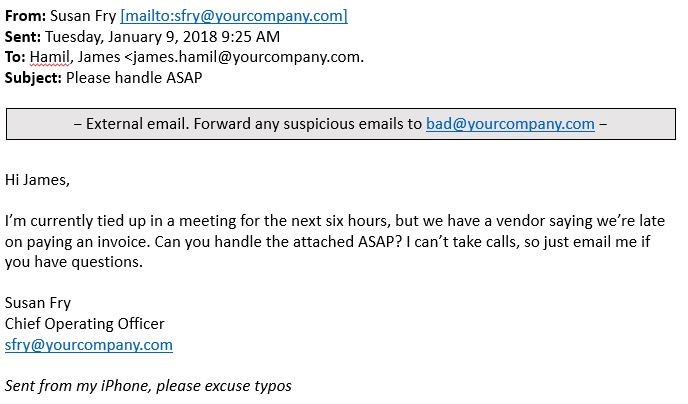

What This Scam Is
Business Email Compromise is a corporate-targeted scam where criminals impersonate vendors, executives, or finance officers to redirect large payments.
How It Works
- Hacker gains access to corporate email (via phishing or malware).
- Fraudster monitors communications silently for weeks.
- When a legitimate invoice is due, criminal sends altered bank details.
- Finance department transfers funds to fraudster’s account.
Funds are quickly moved across multiple accounts.
Why It’s So Dangerous
• High-value transactions
• Appears as normal business communication
• Often undetected until month-end reconciliation
Real Example
NICE Actimize fraud analysis:
https://www.niceactimize.com/blog/fraud-the-next-frontier-of-fraud-prevention-in-commercial-banking
Financial Impact
Global BEC losses annually run into billions of dollars, with individual transactions often exceeding $100,000 or more.
How to Stay Safe
• Confirm vendor bank changes via phone
• Use dual-authorization for payments
• Enable email multi-factor authentication
• Conduct vendor validation audits
8. Insider Collusion in Banking and Cash Logistics



What This Scam Is
Insider collusion occurs when bank employees, contractors, or cash logistics staff assist criminals in executing fraud.
How It Works
- Insider shares route schedules or system credentials.
- Controls are bypassed internally.
- Cash or funds are stolen with minimal suspicion.
Insider participation reduces security friction.
Why It’s Dangerous
• Hard to detect
• Trusted employee access
• Enables large-scale theft
Real Example
NDTV coverage of Bengaluru heist investigation:
https://www.ndtv.com/india-news/bengaluru-cash-van-heist-case-cracked-3-arrested-rs-5-76-crore-recovered-9681356
Financial Impact
Insider-related fraud often results in larger losses because internal controls are knowingly exploited.
How to Stay Safe
For Banks:
• Segregation of duties
• Access log monitoring
• Behavioral analytics for employee transactions
• Whistleblower channels
9. ATM Black Box Attacks (ATM Jackpotting)



What This Scam Is
ATM black box attacks involve physically tampering with an ATM to force it to dispense cash without using a valid card.
How It Works
- Criminal opens ATM cabinet (often using stolen keys).
- Internal cable connected to dispenser is detached.
- External “black box” device attached.
- Device sends command to release cash.
In malware-based jackpotting, ATM software is infected.
Why It’s Effective
• Immediate large cash payout
• Limited transaction traceability
• Coordinated attacks across cities
Real Example
Industry fraud prevention insights:
https://www.niceactimize.com/blog/fraud-the-next-frontier-of-fraud-prevention-in-commercial-banking
Financial Impact
Losses can range from lakhs to crores per coordinated operation.
How to Stay Safe
For Banks:
• Install anti-tamper alarms
• Regular ATM inspection
• Encrypted dispenser communication
• Real-time anomaly alerts
For Customers:
• Avoid visibly damaged ATMs
• Report suspicious behavior
10. SIM Swap Fraud



What This Scam Is
SIM swap fraud allows criminals to take over a victim’s phone number to intercept OTPs and banking alerts.
How It Works
- Personal data gathered from phishing or leaks.
- Fraudster contacts telecom provider posing as victim.
- SIM replacement approved.
- Victim’s phone loses signal.
- Fraudster resets banking credentials.
- Funds transferred out.
Why It’s So Dangerous
• Bypasses SMS-based 2FA
• Victim unaware until funds disappear
• Often combined with phishing
Real Example
NDTV SIM-box fraud bust:
https://www.ndtv.com/andhra-pradesh-news/massive-international-sim-box-technology-cyber-fraud-busted-in-andhra-pradesh-9984336
Financial Impact
Complete account takeover can empty savings, credit lines, and linked wallets.
How to Stay Safe
• Activate SIM lock or port freeze
• Use authenticator apps instead of SMS OTP
• Immediately report sudden network loss
• Monitor account activity alerts
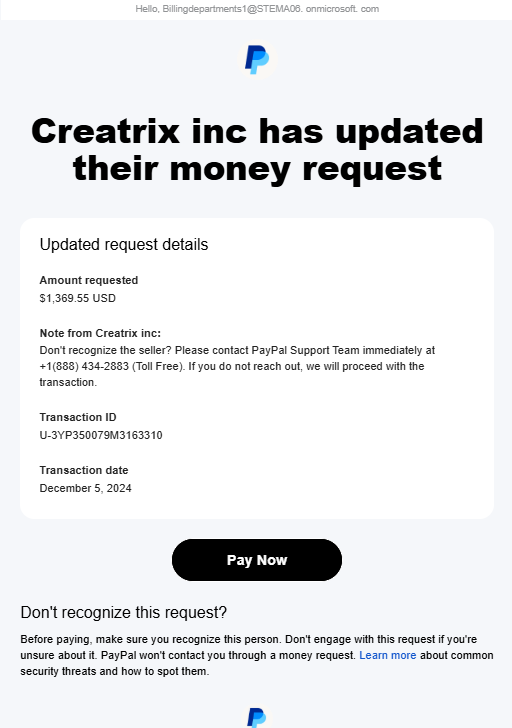
11. Crypto Exchange Exit Scams
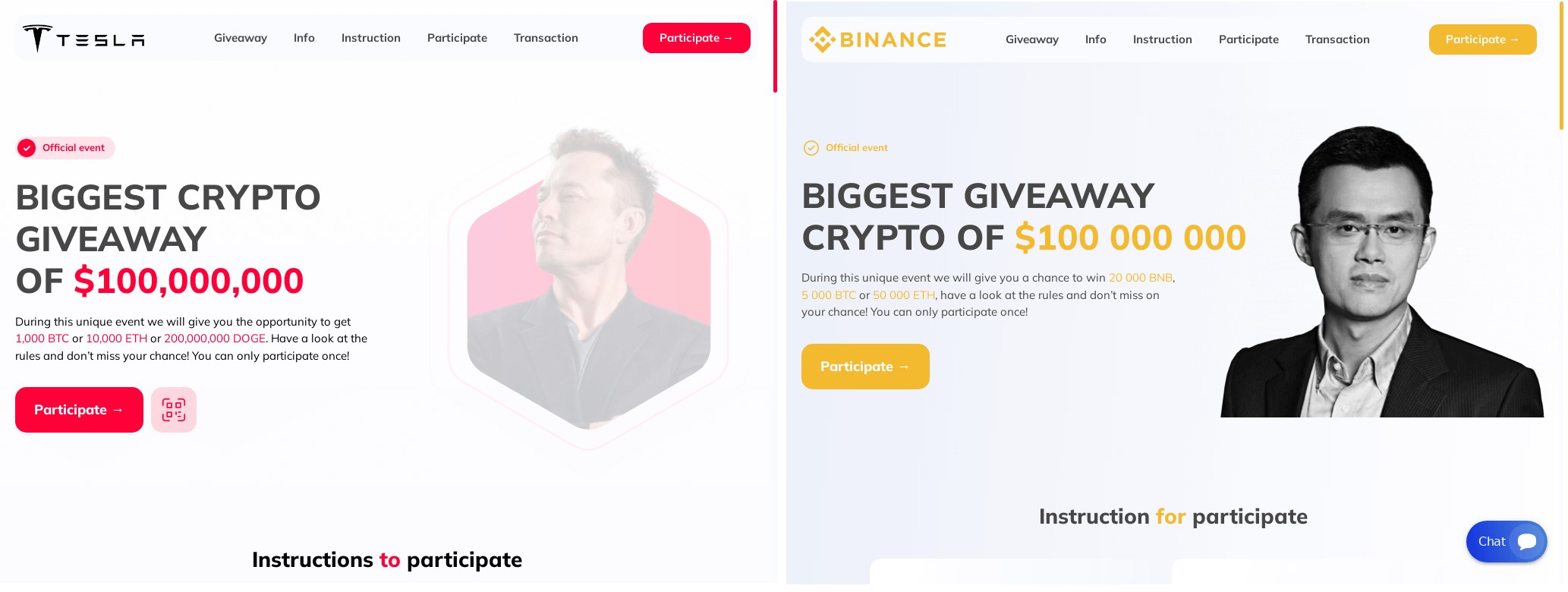
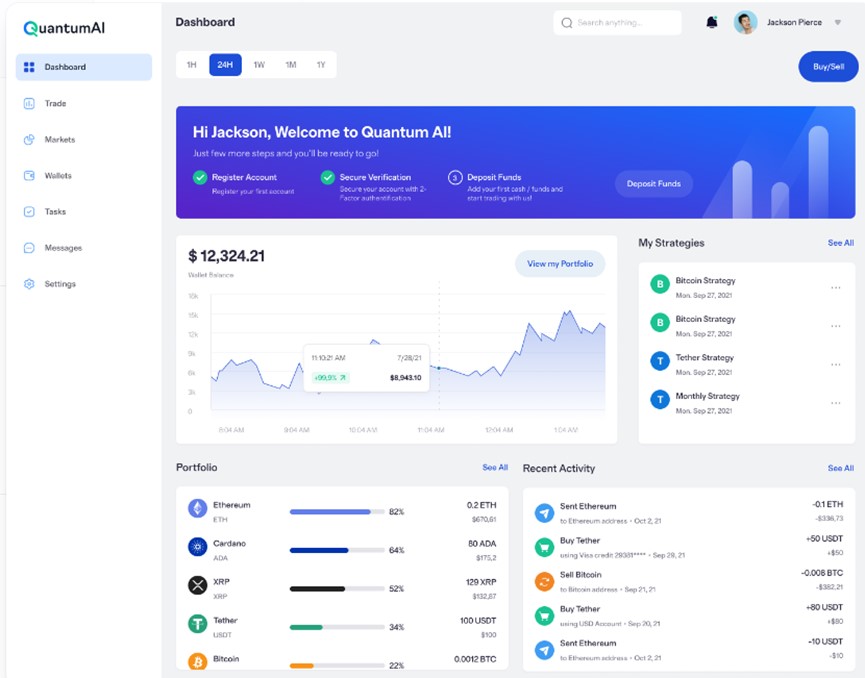

What This Scam Is
Crypto exchange exit scams, often called “rug pulls,” occur when fraudulent cryptocurrency trading platforms collect deposits from users and suddenly shut down operations, disappearing with investors’ funds.
In 2026, these scams increasingly intersect with banking systems because victims fund crypto wallets using direct bank transfers, debit cards, or UPI-linked gateways.
How the Scam Works
- Fraudsters launch a professional-looking exchange website.
- Social media ads or influencers promote “high returns.”
- Victims deposit money via bank transfer.
- Platform displays fake trading profits.
- Withdrawal requests are delayed or denied.
- Website disappears and funds are moved to untraceable wallets.
Why It’s Effective
• Sophisticated user interfaces create trust
• Fake testimonials and manipulated trading charts
• Global operations make legal recovery difficult
• Victims see initial “profits,” encouraging higher deposits
Real Example
Chainalysis Crypto Scam Report 2026:
https://www.chainalysis.com/blog/crypto-scams-2026/
Financial Impact
Many victims lose life savings. In large-scale cases, losses reach hundreds of millions globally.
How to Stay Safe
For Individuals:
• Use exchanges registered with financial regulators
• Verify company leadership and physical office
• Avoid platforms guaranteeing fixed returns
• Never pay additional “withdrawal tax” or “unlock fee”
For Banks:
• Monitor high-risk transfers to newly created crypto platforms
• Implement transaction velocity alerts
12. Fake Loan Apps and Digital KYC Fraud

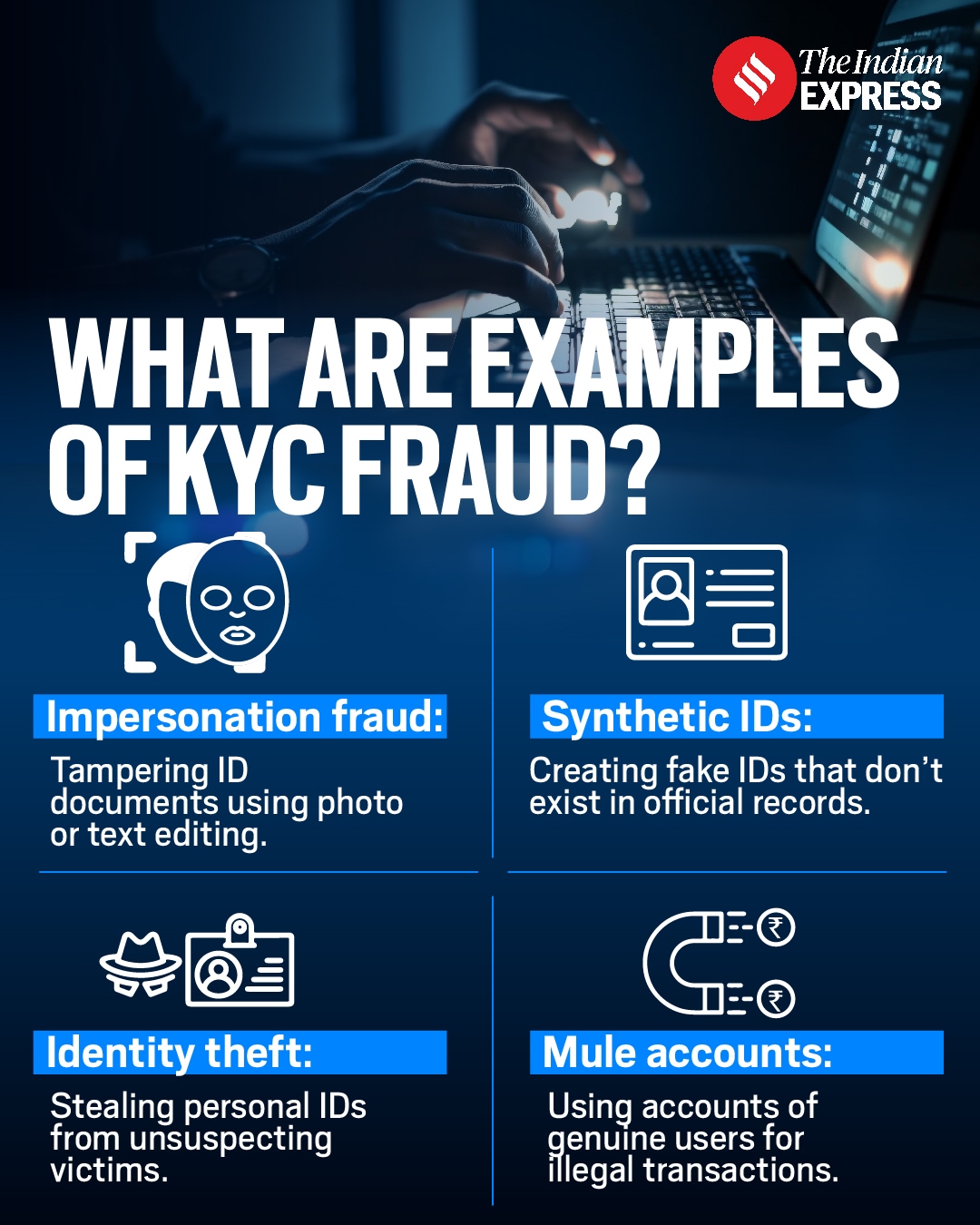

What This Scam Is
Fake loan apps promise instant approval but instead harvest personal data, misuse KYC documents, and extort victims.
How the Scam Works
- Victim downloads app offering quick loan approval.
- App requests access to contacts, gallery, and identity documents.
- Either no loan is disbursed or small amount is credited.
- Excessive interest and hidden charges are demanded.
- Victims are threatened with public humiliation if they do not pay.
In many cases, identity documents are later used to open mule bank accounts.
Why It’s Effective
• Targets financially vulnerable individuals
• Exploits urgent financial needs
• Uses intimidation tactics
• Harvests reusable identity data
Real Example
Times of India case involving loan app fraud:
https://timesofindia.indiatimes.com/city/hyderabad/ayurvedic-doctor-loses-over-36-lakh-to-loan-app-fraud/articleshow/128006410.cms
Financial Impact
Victims suffer both direct financial loss and long-term identity misuse risks.
How to Stay Safe
For Individuals:
• Check if lender is registered with RBI or local regulator
• Do not grant unnecessary app permissions
• Never share full KYC documents with unknown apps
• Report harassment to cybercrime authorities
For Banks:
• Strengthen KYC verification
• Flag multiple new accounts using similar device fingerprints
13. SWIFT Payment Manipulation Attempts




What This Scam Is
SWIFT manipulation scams involve attempts to send unauthorized high-value international wire transfers by exploiting compromised banking credentials.
How the Scam Works
- Fraudster infiltrates bank or corporate network via phishing.
- Gains access to treasury or payment authorization systems.
- Initiates large cross-border transfers.
- Funds are routed to offshore shell companies.
Even failed attempts cause severe disruption and financial risk.
Why It’s Dangerous
• High transaction values
• Cross-border jurisdiction complexity
• Severe reputational damage
• Potential regulatory penalties
Real Example
SWIFT fraud advisory:
https://www.swift.com/risk-and-compliance/fraud/payments-fraud
Financial Impact
Single unauthorized transfers can exceed millions of dollars.
How to Stay Safe
For Banks:
• Multi-layer approval workflows
• Network segmentation
• Endpoint protection and zero-trust architecture
• Real-time transaction anomaly detection
For Corporates:
• Separate treasury credentials
• Conduct regular cyber audits
14. Real Estate Wire Fraud



What This Scam Is
Real estate wire fraud targets property buyers during closing transactions, redirecting large payments to fraudulent accounts.
How the Scam Works
- Fraudster hacks real estate agent or lawyer’s email.
- Monitors ongoing property deal.
- Just before closing, sends “updated bank details.”
- Buyer transfers large amount to scam account.
Funds are immediately withdrawn or converted to crypto.
Why It’s Effective
• High-value property transactions
• Time-sensitive closings
• Email appears legitimate
Real Example
Escrow fraud advisory:
https://dfpi.ca.gov/regulated-industries/escrow-law/online-escrow-companies/online-escrow-fraud-questions-answers/
Financial Impact
Victims often lose entire property deposits.
How to Stay Safe
For Buyers:
• Confirm bank details via phone using official contact number
• Never rely solely on email instructions
For Real Estate Firms:
• Enforce secure email authentication
• Educate clients about wire fraud risks
15. Instant Payment Rail Exploitation




What This Scam Is
Fraud exploiting real-time payment systems where funds settle instantly and cannot be reversed.
How the Scam Works
- Fraudster creates urgency (bank alert, parcel scam, tax notice).
- Victim sends instant transfer via UPI or real-time payment system.
- Funds are immediately layered across accounts.
- Withdrawal or crypto conversion within minutes.
Why It’s So Dangerous
• No recovery window
• Faster than fraud detection systems
• High psychological pressure
Real Example
Instant payment regulation overview:
https://technoxander.com/instant-payments-regulation-guidelines/
Financial Impact
Increasing share of total banking fraud losses due to speed.
How to Stay Safe
For Individuals:
• Pause before high-value instant transfers
• Set daily transaction limits
• Enable SMS/email alerts
For Banks:
• Introduce cooling-off periods for high-risk transactions
• Use behavioral analytics
• Implement transaction delay triggers for unusual activity
Banking Scams 2026: Detailed Investigation of Scams 16 to 20
Vendor Spoofing, Government Impersonation, Elder Exploitation, Gift Card Laundering & Hybrid Social-Crypto Fraud
Meta Description:
A detailed investigative breakdown of five major banking scams of 2026 — Vendor Identity Spoofing, Government Official Impersonation, Elder Financial Exploitation, Gift Card Laundering, and Hybrid Social Media + Banking + Crypto Scams — including how they work, real examples, financial impact, and complete prevention strategies.
16. Vendor Identity Spoofing (Supplier Payment Redirection Fraud)



What This Scam Is
Vendor identity spoofing is a corporate banking fraud where criminals impersonate legitimate suppliers and trick companies into updating bank details for invoice payments.
This scam is closely related to Business Email Compromise but focuses specifically on supplier payment manipulation.
How the Scam Works
- Criminals research a company’s vendor ecosystem.
- They create a spoofed email domain (for example, replacing one letter in the vendor’s official email).
- The finance department receives a message stating that the supplier has “updated banking details.”
- Payment records are changed internally.
- Upcoming invoices are paid to the fraudster’s account.
- Funds are layered through mule accounts and withdrawn quickly.
Why It’s So Effective
• Email appears legitimate
• Timing often coincides with genuine invoice cycles
• Finance teams process high volumes and may skip verification
• Changes are small and seem routine
Real Example
Commercial banking fraud insights:
https://www.niceactimize.com/blog/fraud-the-next-frontier-of-fraud-prevention-in-commercial-banking
Financial Impact
Individual cases often exceed $100,000 per payment cycle. Large corporations have lost millions before detecting the fraud.
How to Stay Safe
For Businesses:
• Mandatory verbal verification for vendor bank changes
• Two-person approval for payment detail updates
• Vendor change audit logs
• Email domain monitoring tools
For Banks:
• Monitor first-time payments to new accounts
• Flag unusual account-opening patterns linked to vendor fraud
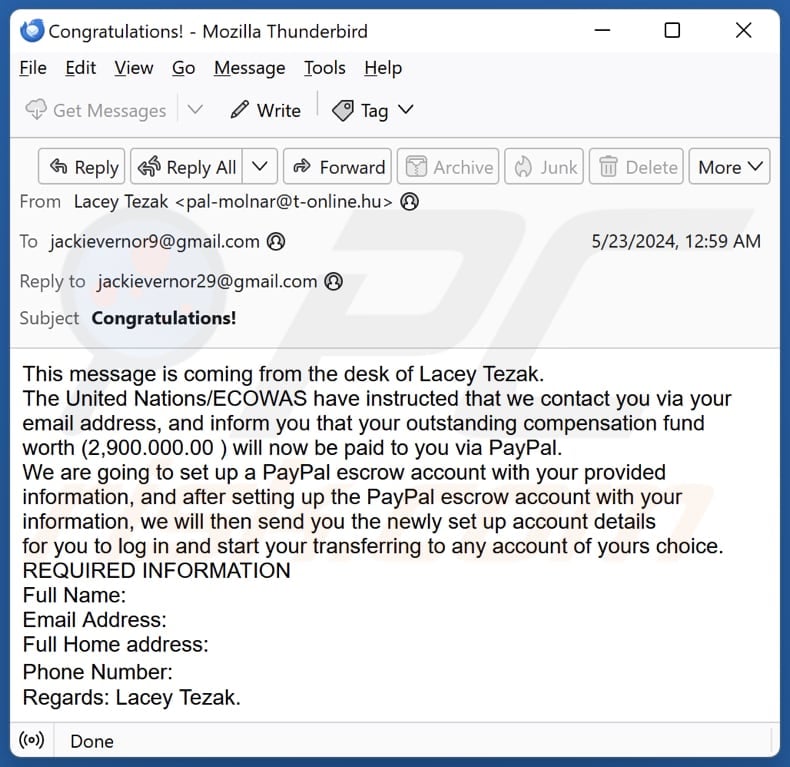
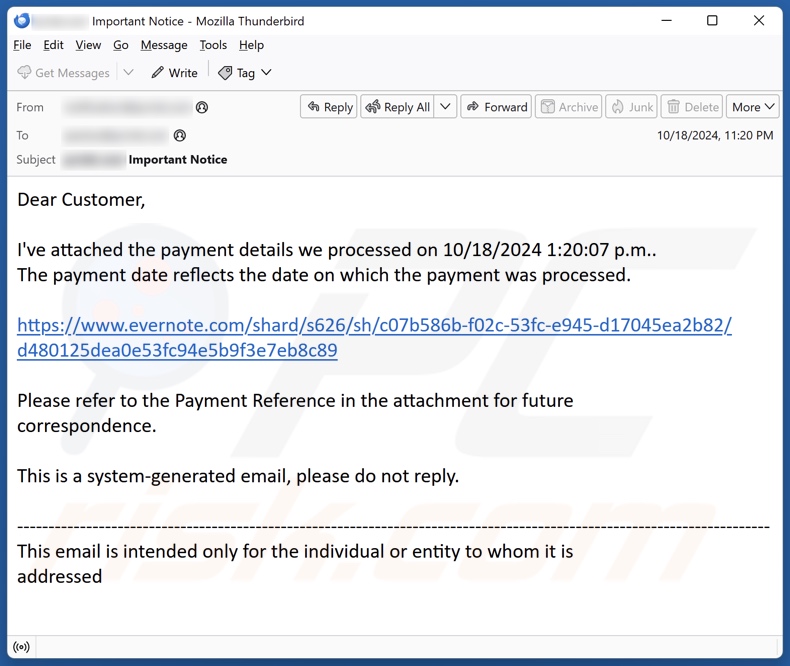
17. Government Official Impersonation Scams
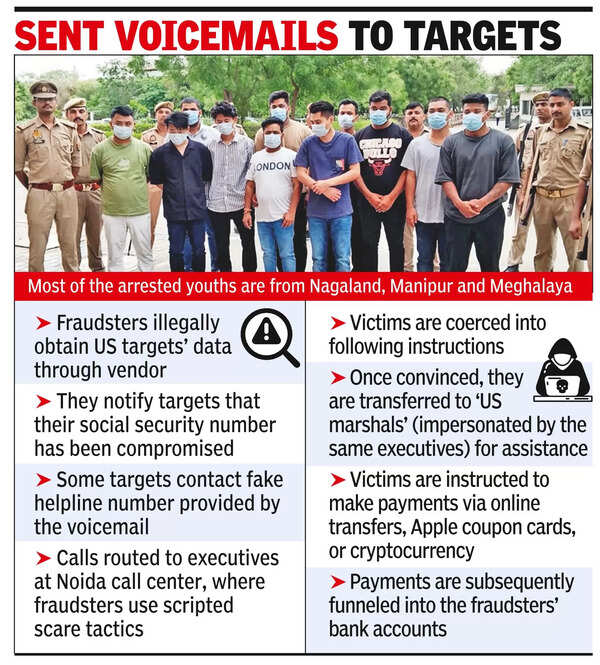

What This Scam Is
Fraudsters impersonate law enforcement, tax officials, or central bank authorities to intimidate victims into transferring funds.
This scam relies heavily on fear and authority psychology.
How the Scam Works
- Victim receives a call claiming involvement in a criminal case.
- Caller claims to be from police, tax department, or cybercrime division.
- Victim is told funds must be transferred to “verify account legality.”
- Victim complies under fear of arrest or penalty.
- Funds are immediately routed and withdrawn.
Why It’s So Effective
• Authority bias
• Fear-induced urgency
• Official-sounding documentation and IDs
• Use of caller ID spoofing
Real Example
Reuters investigation into scam compound operations:
https://www.reuters.com/world/china/scammers-abandoned-cambodia-compound-exposes-brutality-banality-fraud-2026-02-06/
Financial Impact
Losses can range from small amounts to entire savings accounts, especially in high-pressure digital arrest scams.
How to Stay Safe
For Individuals:
• Government agencies do not demand payments over phone
• Verify notices via official government portals
• Never share OTP or transfer money under threat
For Banks:
• Flag unusual large transfers following suspicious call patterns
• Customer education campaigns
18. Elder Financial Exploitation




What This Scam Is
Targeted financial exploitation of elderly individuals through emotional manipulation and impersonation.
How the Scam Works
Common methods include:
• “Grandparent scam” — Caller pretends to be a grandchild in emergency
• Tech support scam — Fake virus warning demanding payment
• Romance scam — Long-term emotional grooming
Fraudsters rely on limited digital literacy and high trust levels.
Why It’s Dangerous
• Seniors often hold significant retirement savings
• Emotional vulnerability
• Delayed detection
Real Example
FDIC advisory on scams targeting older adults:
https://www.fdic.gov/consumer-resource-center/2025-07/scams-targeting-older-adults
Financial Impact
Many elderly victims lose lifetime savings.
How to Stay Safe
For Families:
• Monitor unusual transactions
• Set transaction alerts
• Educate elderly relatives about common scams
For Banks:
• Add senior account monitoring flags
• Offer fraud-awareness workshops
19. Gift Card Laundering Scams


What This Scam Is
Fraudsters instruct victims to purchase high-value gift cards and share the codes, allowing criminals to convert funds into anonymous assets.
How the Scam Works
- Victim receives urgent call (tech support, IRS, police, parcel scam).
- Told to purchase gift cards immediately.
- Victim shares card codes over phone.
- Fraudster redeems cards instantly or resells them online.
Gift cards are hard to trace and nearly impossible to reverse.
Why It’s Effective
• Quick conversion to untraceable value
• No banking reversal mechanism
• Often used in conjunction with other scams
Real Example
Fintech Global analysis on prepaid card risk:
https://fintech.global/2026/02/02/why-prepaid-gift-cards-are-a-growing-financial-crime-risk/
Financial Impact
Individual losses vary from thousands to lakhs, often affecting vulnerable victims.
How to Stay Safe
• No legitimate authority demands gift card payment
• Retailers should limit high-value bulk purchases
• Never share gift card codes
20. Hybrid Social Media + Banking + Crypto Scams




What This Scam Is
A multi-stage scam that begins on social media or dating apps and ends with funds being moved through bank transfers into cryptocurrency wallets.
How the Scam Works
- Fraudster creates attractive fake profile.
- Emotional connection is built over weeks.
- Investment opportunity introduced.
- Victim transfers money via bank to crypto platform.
- Funds are moved across wallets and disappear.
This is a convergence scam combining romance fraud, banking fraud, and crypto laundering.
Why It’s So Dangerous
• Emotional manipulation lowers suspicion
• Crypto conversion prevents recovery
• Cross-border operations limit enforcement
Real Example
ET Edge Insights on romance-investment scams:
https://etedge-insights.com/technology/cyber-security/love-in-the-age-of-identity-frauds-how-dating%E2%80%91app-culture-super%E2%80%91charged-romance-scams-in-2025/
Financial Impact
Victims often invest progressively larger sums after seeing fake profits. Ensure you dont get caught in greed as no one will offer you money online. If some stranger is offering you a offer that can give you financial advantage, than 99.99999 % its a scam, there are more chances of a germ surviving detol soap wash than someone offering you (a stranger) free money. Remember that
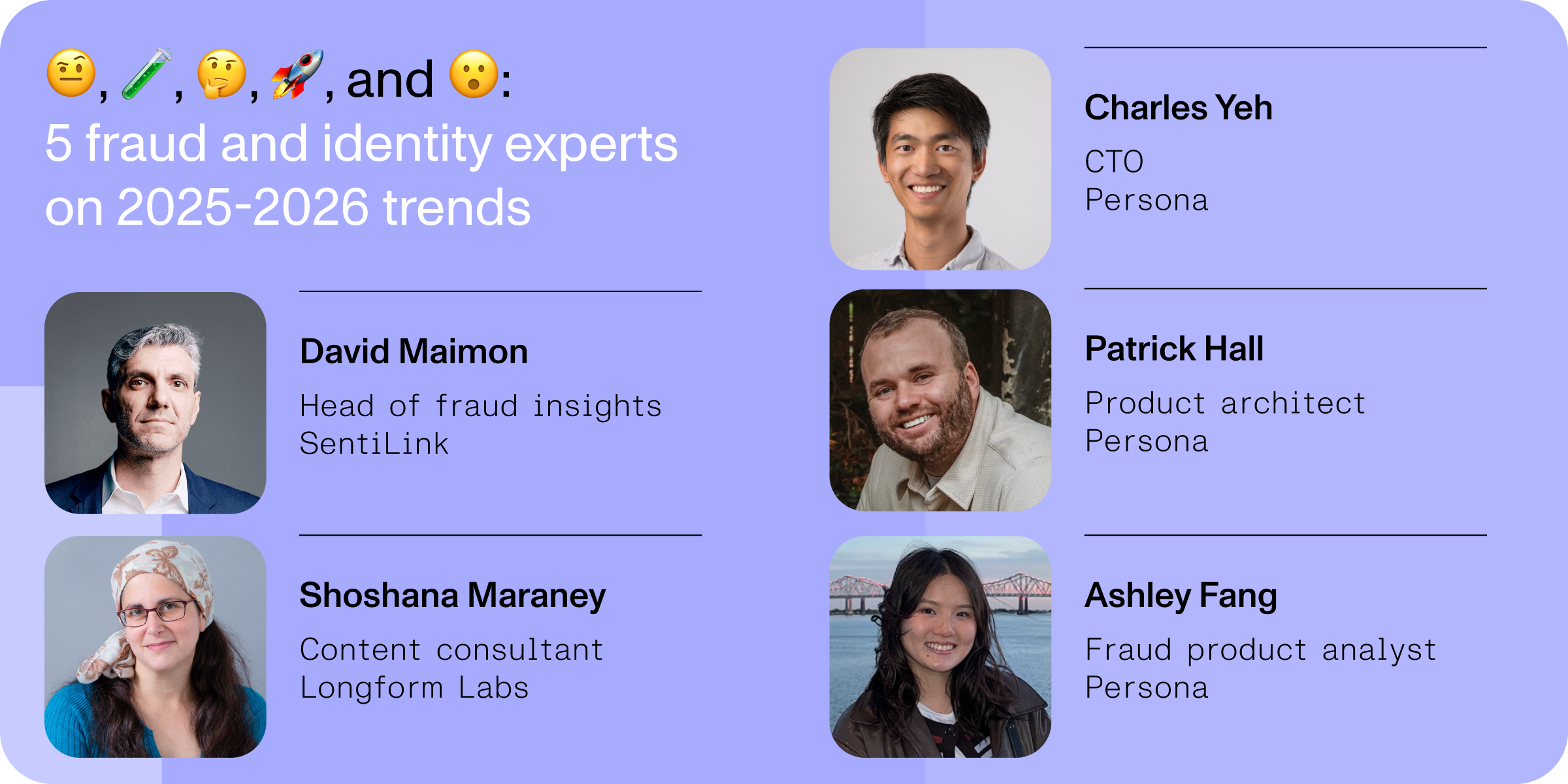
Final Conclusion
The 2026 banking fraud landscape shows convergence of technology, psychology, and financial system loopholes. The biggest risks arise from urgency, emotional manipulation, and instant payment rails.
For individuals: pause, verify, and distrust urgency. Never share yuour OTP with anyone and never trust anyone over a call, if yiou get a call from bank – personally visit the bank branch.
For banks: strengthen behavioral analytics, insider risk controls, and transaction friction for high-risk payments. Ensure Cyber security guidelines are followed by all employees.
Here is a fully SEO-optimized FAQ section for your complete article covering all 20 banking scams of 2026. These questions are structured to target featured snippets, “People Also Ask” results, and long-tail search queries.
Frequently Asked Questions (FAQ) – 20 Largest Banking Scams of 2026
1. What are the biggest banking scams in 2026?
The biggest banking scams in 2026 include transnational scam compounds, Authorized Push Payment (APP) fraud, pig-butchering crypto scams, deepfake voice fraud, SIM swap attacks, ATM black box attacks, fake loan apps, vendor payment redirection fraud, and hybrid social-media-to-crypto scams.
These scams combine psychological manipulation, instant digital payments, AI impersonation, and cross-border money laundering networks, making them more dangerous than traditional fraud methods.
2. Why are banking scams increasing in 2026?
Banking scams are increasing due to:
• Growth of instant payment systems
• Increased digital banking adoption
• AI tools enabling deepfake impersonation
• Cryptocurrency making money laundering easier
• Large-scale organized scam networks
Fraudsters are exploiting speed and trust in digital financial systems.
3. What is Authorized Push Payment (APP) fraud?
APP fraud occurs when a victim is tricked into voluntarily transferring money to a scammer. The fraudster impersonates a bank official, police officer, tax authority, or business partner and creates urgency to move funds.
Because the victim authorizes the transaction, recovery becomes difficult.
4. What is pig-butchering crypto scam?
Pig-butchering is a long-term romance or friendship scam where victims are emotionally groomed before being convinced to invest in fake cryptocurrency platforms.
Victims initially see fake profits and later lose large amounts when the platform blocks withdrawals.
5. How does SIM swap fraud work?
SIM swap fraud happens when criminals convince a telecom provider to transfer a victim’s phone number to a new SIM card controlled by the fraudster.
Once activated, scammers receive OTPs and banking alerts, allowing them to reset passwords and drain accounts.
6. What is deepfake voice fraud in banking?
Deepfake fraud uses artificial intelligence to clone someone’s voice. Criminals impersonate executives or customers over phone calls to authorize financial transactions.
This bypasses traditional voice verification systems.
7. What are ATM black box attacks?
ATM black box attacks involve physically tampering with ATMs to force them to dispense cash without a card.
Criminals connect external devices to the ATM’s internal systems, triggering unauthorized withdrawals.
8. What is Business Email Compromise (BEC)?
BEC is a corporate fraud where hackers infiltrate email accounts and redirect invoice payments to fraudulent bank accounts.
It primarily targets companies and finance departments handling high-value payments.
9. How do crypto exchange exit scams work?
In crypto exit scams, fake exchanges collect deposits from users and suddenly shut down operations, disappearing with investors’ funds.
These scams often show fake profits before vanishing.
10. What is vendor identity spoofing?
Vendor spoofing occurs when fraudsters impersonate legitimate suppliers and request bank detail changes, redirecting payments to scam accounts.
This type of fraud is common in corporate payment systems.
11. How does real estate wire fraud happen?
Real estate wire fraud occurs when hackers intercept property transaction emails and send fake bank instructions just before closing.
Buyers unknowingly transfer large property deposits to fraudulent accounts.
12. What is instant payment exploitation?
Instant payment exploitation happens when scammers pressure victims to send money through real-time payment systems like UPI or RTP, leaving no recovery window once funds are transferred.
13. How do fake loan apps scam people?
Fake loan apps promise instant approval but instead collect identity documents, charge excessive hidden fees, or blackmail victims using personal data.
Some also misuse KYC documents to open mule accounts.
14. What is government impersonation scam?
In this scam, criminals pretend to be police officers, tax authorities, or cybercrime officials and threaten victims into transferring money to “verify accounts” or avoid arrest.
Legitimate authorities never demand payment over phone calls.
15. What is elder financial exploitation?
Elder financial exploitation targets senior citizens using emotional manipulation, emergency scams, romance scams, or tech support fraud.
Victims often lose retirement savings.
16. Why are gift card scams common in 2026?
Gift cards are difficult to trace and nearly impossible to reverse once redeemed. Fraudsters instruct victims to buy gift cards and share codes to convert stolen funds quickly.
No legitimate authority asks for gift card payments.
17. What are money mule networks?
Money mule networks involve individuals who allow their bank accounts to be used to transfer stolen funds.
These networks help fraudsters hide transaction trails and avoid detection.
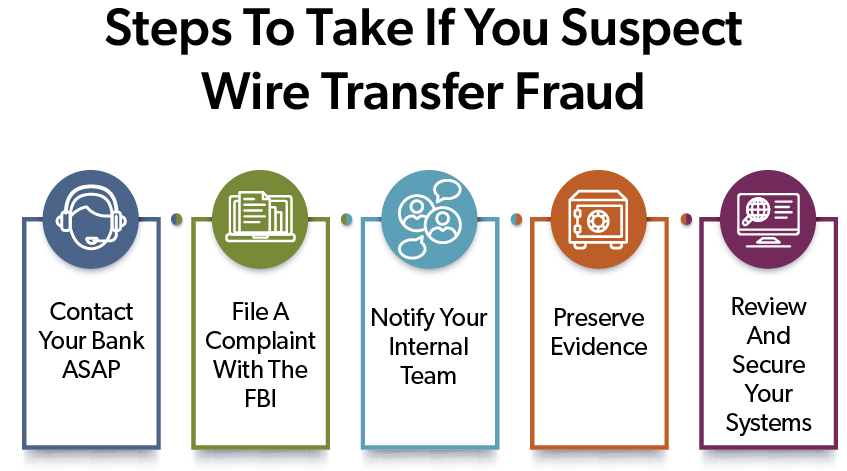
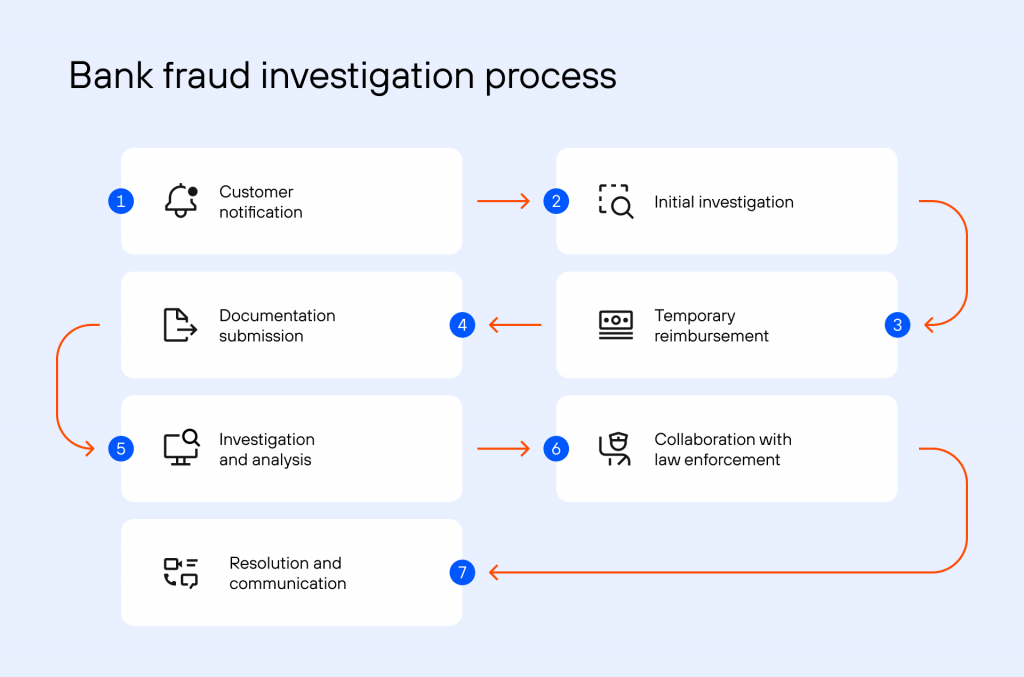
18. What should I do if I become a banking fraud victim?
If you suspect fraud:
• Immediately contact your bank
• Block cards and accounts
• File a complaint with cybercrime authorities
• Preserve call logs, screenshots, and transaction details
The faster you report, the higher the chance of fund recovery.
19. How can I protect my bank account from fraud in 2026?
To stay safe:
• Use multi-factor authentication
• Enable transaction alerts
• Avoid sharing OTPs
• Verify before large transfers
• Do not act under urgency
• Use authenticator apps instead of SMS OTP
Layered security is essential.
20. Are crypto scams increasing in 2026?
Yes. Crypto-related scams, including pig-butchering, fake exchanges, and hybrid social-media scams, are rising due to anonymity, global access, and difficulty in reversing transactions.
21. Which banking scam causes the highest losses?
Pig-butchering crypto scams and large-scale corporate BEC fraud often cause the highest individual losses, sometimes reaching millions per victim or transaction.
22. Can banks reverse scam transactions?
Reversal depends on:
• Type of transaction
• Speed of reporting
• Whether funds have been withdrawn or converted
Instant payments and crypto transfers are harder to reverse.
Cyber complaints also help banks to ensure justice is served. If you ever suffer from scam, ensure you lodge a complaint with cyber police at the earliest.